-

Checking Kubernetes pod CPU and memory
-

Alternative Kubernetes dashboards
-

Live updates of Kubernetes objects during deployment
-

Choosing a container platform
-

A beginner's guide to containers
-
Deploying to Azure with GitHub Actions and Octopus
-
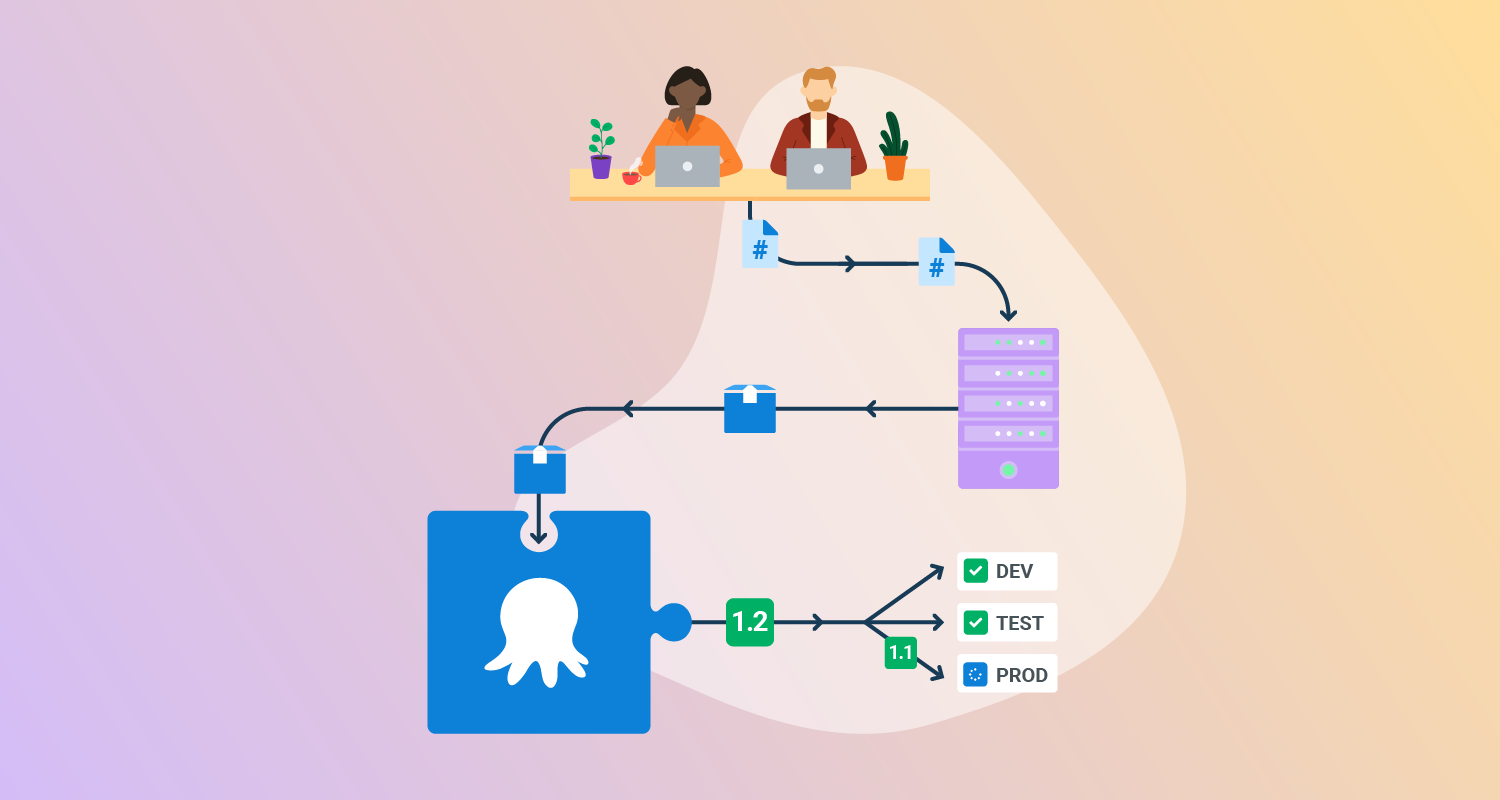
How Octopus complements your build server
-

Using variables for Kubernetes without breaking YAML
-

DevOps uses a capability model, not a maturity model
-

Inside DevOps with Stephen Shamakian
-

10 of our favorite actions for GitHub Actions
-

Multi-environment deployments with GitHub Actions and Octopus
Articles - Page 22
Related posts

Connecting an AWS EKS Argo CD instance to Octopus Cloud
Learn how to connect an AWS EKS Argo CD instance to Octopus Deploy.

Financial industry compliance, the DevOps way
Find out how to apply DevOps thinking to financial industry regulation and compliance.

Continuous Delivery Office Hours Ep.4: Mono, micro, mesco
Explore the trade-offs between majestic monoliths, microservices, and mescoservices in this episode of Continuous Delivery Office Hours, including how team structures influence architectural choices.








